Imagine testing software like pushing every door in a building to see which ones creak, jam, or open unexpectedly. That’s what fuzz testing does—but for code. It deliberately feeds a system random, malformed, or unexpected inputs to find hidden cracks before malicious hackers do. It’s chaos engineered with purpose, uncovering vulnerabilities that structured tests often overlook.
Let’s explore how fuzz testing became one of the most powerful methods for fortifying software against the unpredictable nature of real-world use.
The Philosophy Behind Fuzzing
In traditional testing, we often check what we expect the system to do. Fuzz testing flips this on its head—it explores the unexpected. Think of it as throwing pebbles at a glass wall to find weak spots before a storm shatters it.
This unconventional method relies on generating massive volumes of random data—“fuzz”—and feeding it into software inputs to trigger crashes, leaks, or unusual behaviour. By analysing these reactions, developers identify vulnerabilities buried deep within the code.
For learners mastering advanced testing techniques, enrolling in software testing coaching in pune offers exposure to how fuzz testing integrates with modern DevSecOps pipelines and automated testing frameworks.
How Fuzz Testing Works: The Chaos with a Plan
At its core, fuzz testing involves three stages: input generation, execution, and monitoring.
- Input Generation: Specialised tools create malformed or randomised inputs.
- Execution: These inputs are fed into the program to observe its behaviour.
- Monitoring: Any abnormal responses—like crashes, exceptions, or memory leaks—are recorded for analysis.
Modern fuzzing tools, such as AFL (American Fuzzy Lop) and libFuzzer, use intelligent mutation algorithms that learn from past results, refining their inputs to probe deeper with every cycle. The result? A near-endless cycle of smart chaos designed to expose weak spots long before attackers can exploit them.
Real-World Applications of Fuzzing
Fuzz testing has a long and impressive track record in software security. It’s been responsible for uncovering vulnerabilities in some of the world’s most widely used systems—browsers, operating systems, and even security libraries themselves.
For example, Google’s OSS-Fuzz continuously runs fuzzing campaigns on open-source projects, finding thousands of bugs before they reach end-users. Similarly, Microsoft employs large-scale fuzz testing across its applications, saving millions by preventing critical exploits.
For professionals entering the field, understanding such methodologies through structured software testing coaching in pune provides real-world insight into how fuzzing supports secure software development.
Challenges in Fuzz Testing
Despite its power, fuzz testing isn’t without challenges. Generating meaningful random inputs for complex systems requires a deep understanding of data formats and protocols. Simple random data may never reach the system’s deeper logic layers.
Moreover, analysing the flood of crash data can be daunting. Developers must distinguish between false positives, duplicate errors, and truly exploitable vulnerabilities.
Yet, with the rise of machine learning, fuzz testing is evolving. AI-driven fuzzers can predict which parts of the code are more likely to fail, optimising tests for higher efficiency and coverage.
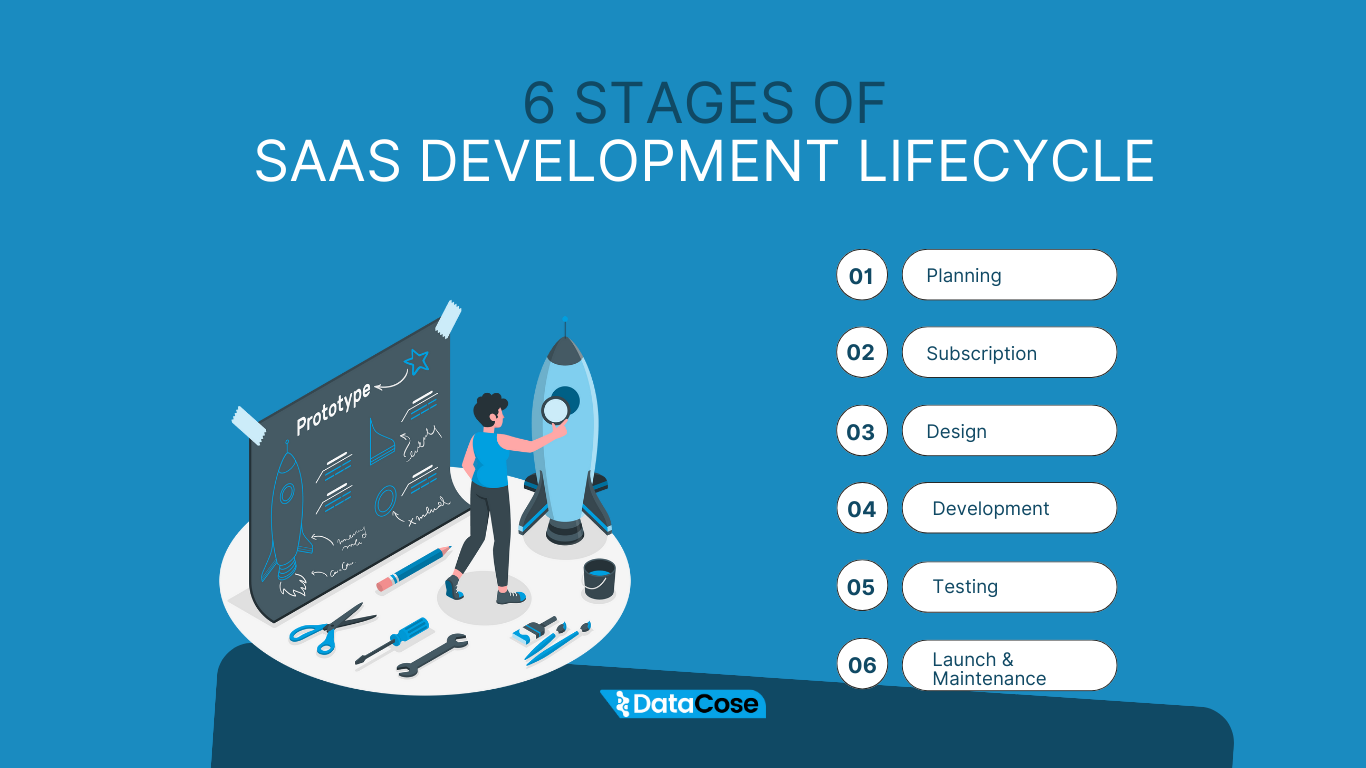
Integrating Fuzz Testing into the SDLC
To get the most out of fuzzing, organisations must treat it as an integral part of the Software Development Life Cycle (SDLC)—not a last-minute audit.
Incorporating fuzzing during continuous integration ensures that vulnerabilities are caught early. Combined with other techniques like static analysis and penetration testing, fuzzing becomes a cornerstone of a proactive security culture.
The key is consistency: the more frequently you “shake the system,” the more resilient it becomes.
Conclusion
Fuzz testing teaches us a vital lesson about software resilience—perfection isn’t achieved by avoiding mistakes but by relentlessly testing for them. By injecting randomness into order, we find the boundaries of robustness and push them further.
As cyber threats grow in sophistication, fuzz testing remains a defender’s secret weapon—a blend of science, creativity, and curiosity. For developers and testers aspiring to strengthen their expertise, mastering such techniques will define their success in safeguarding tomorrow’s digital systems.